# English | [简体中文](./README-zh_CN.md)
# TranSec OS
TranSec OS is a car networking penetration testing distribution system based on Ubuntu 18.04, mainly used for security assessment of car networking devices. The system is equipped with hundreds of dedicated testing tools for vehicle networking security, aiming to solve a series of problems for vehicle networking security practitioners, such as messy testing tools, complex testing environment configuration, and no available tools
## Advantages
An out of the box testing environment that includes hundreds of commonly used toolsets for penetration testing of the Internet of Vehicles. Covering security tests such as reverse engineering, CAN, in car Ethernet, WiFi, Bluetooth, cloud platforms, etc
- Permanent free update support, and gradually increasing the targeted free trial of Anheng's self-developed vehicle networking tools and some commercial software in the future
- An open operating environment that allows users to customize and modify any file or install any program within the system
- Built in various commonly used tools under different architectures such as ARM, X86, MIPS, etc., such as adb, gdb, nmap, busybox, etc
- ...
## Tool List (Partial)
Below are some of the tools listed, and more tools can be explored by yourself.
|Tool Name | Tool Introduction|
|--- | ---|
|CANToolz | CAN Analysis Framework|
|Can Utils | Can's testing toolkit|
|Scapy | Packet Processing Tool|
|Proxmark3 | PM3 client|
|Logic | Logic analyzer client|
|URH | Radio Analysis Tools|
|MQTTclient | MQTT client|
|Gattool | BLE Connection Tool|
|Binwalk | Firmware unpacking and analysis tool|
|IDA Free | Professional binary analysis tool|
|Shambles | Professional binary analysis and vulnerability scanning tool, including automatic unpacking and simulation|
|Ghidra | Open source binary analysis tool|
|Jeb | Android Reverse Analysis Tool|
|Jadx Gui | Open source Android reverse analysis tool|
|Hcitool | Bluetooth Connection Tool|
|Ubertool tools | A software and hardware open-source Bluetooth packet catcher|
|Pybluez2 | Python library - Bluetooth attack tool|
|KillerBee | Security research tool for ZigBee|
|HackRF | HackRF supporting software|
|Frida | hook tool|
|Gdb multiarch | Heterogeneous architecture gdb analysis tool|
|Pwndbg | gdb Advanced Script|
|Pwntools | Python vulnerability exploitation framework|
|QEMU | Open Source Simulator|
|Qemu system | Virtual System Simulator|
|Firmware Mod Kit | Firmware Modification Kit|
|Firmware Analysis Toolkit | An open-source firmware analysis tool|
|Frp | Internal network penetration tool|
|MobSF | Android Automated Static Analysis Tool|
|Burpsuite | Web testing tool|
# Download
- GitHub:[Releases](https://github.com/TianWen-Lab/TranSec/releases)
- Baidu Netdisk:[https://pan.baidu.com/s/1jWFxiawgiC57gLCYiSvnyA](https://pan.baidu.com/s/1jWFxiawgiC57gLCYiSvnyA) password:r4x7
# Installation instructions
This system provides ISO image installation and OVA image import installation methods. It is recommended to use OVA to import virtual machines for simpler and more convenient operations. Due to the large size of the system, importing or installing requires a certain amount of time, which depends on the performance of the disk.
After successful import or installation, boot up and use `iov/root` to login. After successful login, the user experience plan will be displayed, and you can choose to agree or refuse. Once confirmed, you can start using it.

## OVA import
Open the OVA file using virtual machine software:

## ISO installation
When installing using ISO images, **it is recommended to configure 50GB of disk and 4GB of memory**. After loading the image, select 'Boot system install' to enter the installation process:

Enter the password `iov/root` to login to the installation interface:

Enter account password and other information according to the prompts, and click Next to enter the partition process:

After selecting the disk, click Delete to delete the partition:

At this point, a `/dev/sda?` will appear, Select `/dev/sda?`, Click on the arrow

At this point, `/dev/sda` becomes `/dev/sda1`. Select this partition, select the mounted directory (/) and partition format (ext4) from the drop-down menu on the right, and click the arrow again to complete the partition:

Returning to the installation process, after checking the box containing user configuration and data (**must be changed to √**), proceed to the next step to proceed with the installation

The installation time is about 6 minutes. After the progress is completed, click reboot to complete the installation process and enter the system (If you have other things to do, you can do them first. After the system installation is completed, it will automatically restart after 30 seconds ^o^)

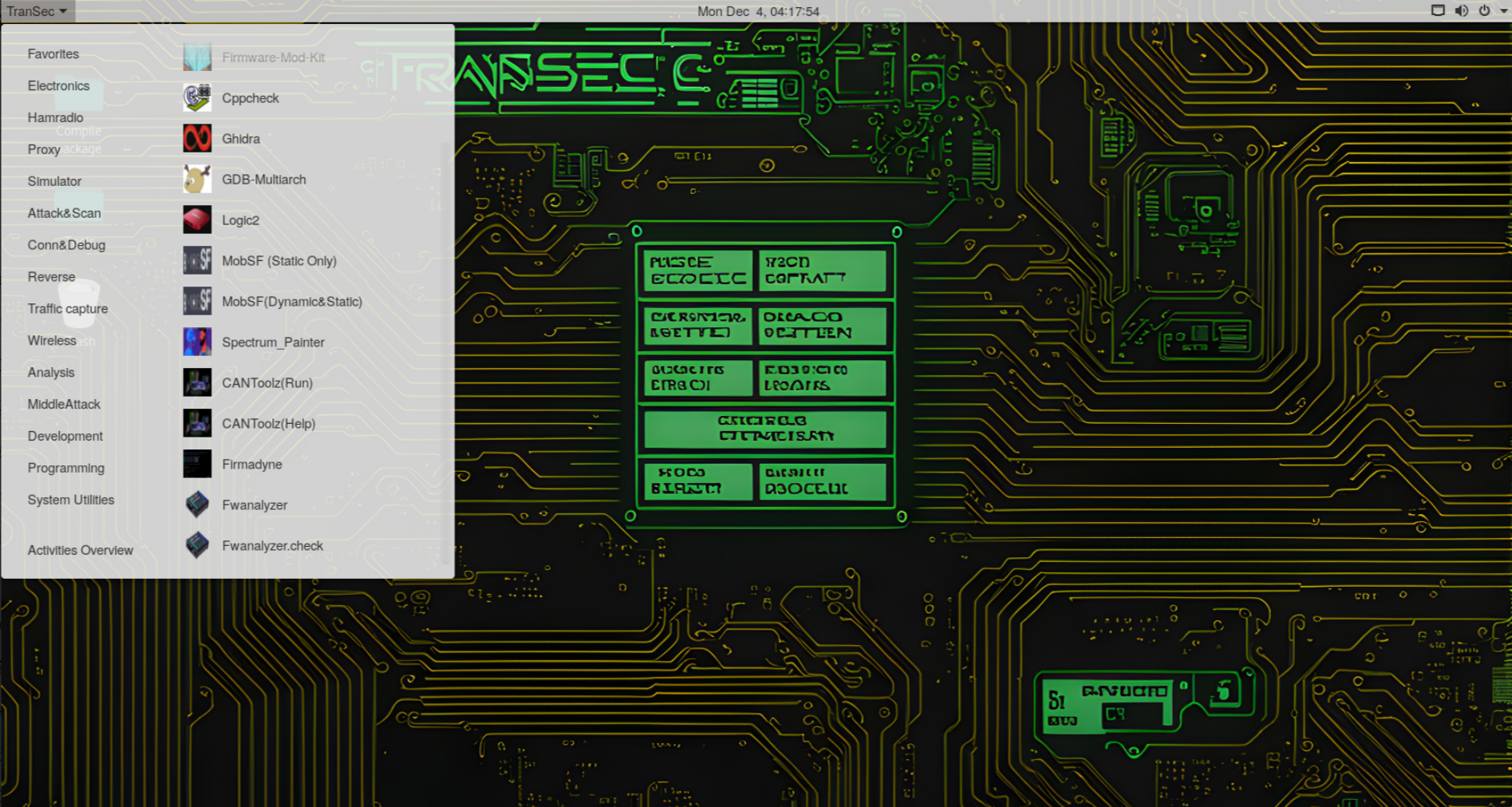
# System screenshot



# Possible installation issues
Due to being based on the `systemback`, there may be some issues during system installation. Below are the corresponding solutions:
1. When using the ISO installation method, when logging into the installation interface, the prompt "Cannot start the Systemback graphical user interface! Unable to connect to the X server" or other reasons for not entering the installation interface may be due to the installation program not starting successfully. It is recommended to shut down the computer first and then try installing again. Please be careful not to restart directly.
2. After importing OVA, it may not be possible to connect to the network. Please restart the system or reconnect to the network in the upper right corner (Wired Connected - Turn Off ->connect).
3. When entering the installation interface or first time and logging into the system for the first time after installation, there will be a long black screen waiting time. This is because there are many services to start, which is a normal phenomenon
# Finally
Thank you for your use. If you have any questions, please provide feedback on ISSUS. We will pay attention to each issue and try to improve it in the next version. Thank you again.
没有合适的资源?快使用搜索试试~ 我知道了~
Internet of Vehicles Penetration testing OS.车联网渗透测试系统,开箱即用的测试环境,...

共4个文件
txt:2个
md:2个
1.该资源内容由用户上传,如若侵权请联系客服进行举报
2.虚拟产品一经售出概不退款(资源遇到问题,请及时私信上传者)
2.虚拟产品一经售出概不退款(资源遇到问题,请及时私信上传者)
版权申诉
0 下载量 107 浏览量
2024-11-29
08:28:46
上传
评论
收藏 8KB ZIP 举报
温馨提示
English | 简体中文传输操作系统TranSec OS是基于Ubuntu 18.04的车联网渗透测试分发系统,主要用于车联网设备的安全评估。系统配备了数百种专用的车联网安全测试工具,旨在解决车联网安全从业者测试工具杂乱、测试环境配置复杂、无可用工具等一系列问题优点开箱即用的测试环境,包含数百种常用的车联网渗透测试工具集。涵盖逆向工程、CAN、车载以太网、WiFi、蓝牙、云平台等安全测试永久免费更新支持,未来将逐步增加安恒自研车联网工具及部分商业软件的针对性免费试用开放的操作环境,允许用户自定义和修改任何文件或安装系统内的任何程序内置ARM、X86、MIPS等不同架构下各种常用工具,如adb、gdb、nmap、busybox等...工具清单(部分)下面列出了一些工具,您可以自行探索更多工具。工具名称 工具介绍CAN工具 CAN分析框架可以使用 Can 的测试工具包斯卡皮 数据包处理工具Proxmark3 PM3 客户端逻辑 逻辑分析仪客户端乌尔格 无线电分析工具MQTT客户端 MQTT 客户端盖特尔 BLE 连接工具宾沃克 固件解
资源推荐
资源详情
资源评论
收起资源包目录
 Internet of Vehicles Penetration testing OS.车联网渗透测试系统,开箱即用的测试环境,包含上百个常见用于车联网渗透测试的工具集。覆盖逆向、CAN、车载.zip (4个子文件)
Internet of Vehicles Penetration testing OS.车联网渗透测试系统,开箱即用的测试环境,包含上百个常见用于车联网渗透测试的工具集。覆盖逆向、CAN、车载.zip (4个子文件)  标签.txt 47B
标签.txt 47B README-zh_CN.md 6KB
README-zh_CN.md 6KB 资源内容.txt 1KB
资源内容.txt 1KB README.md 7KB
README.md 7KB共 4 条
- 1
资源评论

赵闪闪168
- 粉丝: 1746
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜最新资源
- 平面标注法讲解(00G101).ppt
- 学生专用教室设备采购招标文件.doc
- 第五章-昆虫分类学-1.ppt
- 万科同层排水系统示意图.docx
- 管理体系文件2012.4.doc
- 市政工程三方现场安全行为资料台帐.doc
- 工程细部节点做法.doc
- 大学图文信息中心(高层)造价估算指标.doc
- 绿化养护工程项目施工组织设计.pdf
- 基坑支护要点.docx
- 汽轮机零件的强度校核与振动.ppt
- 港口建设项目预可行性研究报告和工程可行性研究报告编制办法.doc
- 大学暑假社会实践总结.doc
- 广东省建设工程标准施工合同.doc
- 中国某石油总公司危机管理预案(008年).doc
- 预算课讲义-脚手架工程.ppt
资源上传下载、课程学习等过程中有任何疑问或建议,欢迎提出宝贵意见哦~我们会及时处理!
点击此处反馈



安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功