cyber forensics-ethical hacking- wireless-hacking.ppt
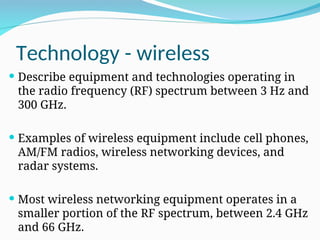
- 2. Technology - wireless Describe equipment and technologies operating in the radio frequency (RF) spectrum between 3 Hz and 300 GHz. Examples of wireless equipment include cell phones, AM/FM radios, wireless networking devices, and radar systems. Most wireless networking equipment operates in a smaller portion of the RF spectrum, between 2.4 GHz and 66 GHz.
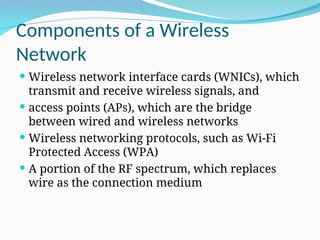
- 3. Components of a Wireless Network Wireless network interface cards (WNICs), which transmit and receive wireless signals, and access points (APs), which are the bridge between wired and wireless networks Wireless networking protocols, such as Wi-Fi Protected Access (WPA) A portion of the RF spectrum, which replaces wire as the connection medium
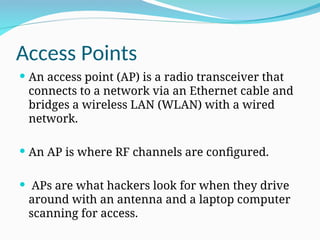
- 4. Access Points An access point (AP) is a radio transceiver that connects to a network via an Ethernet cable and bridges a wireless LAN (WLAN) with a wired network. An AP is where RF channels are configured. APs are what hackers look for when they drive around with an antenna and a laptop computer scanning for access.
- 5. NetStumbler NetStumbler (also known as Network Stumbler) is a tool for Windows that facilitates detection of Wireless LANs using the 802.11b, 802.11a and 802.11g WLAN standards. It runs on Microsoft Windows operating systems from Windows 2000 to Windows XP.
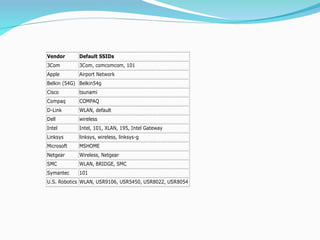
- 6. Service Set Identifiers A service set identifier (SSID) is the name used to identify a WLAN, much the same way a workgroup is used on a Windows network. An SSID is configured on the AP as a unique, 1-to 32-character, case-sensitive alphanumeric name. The AP usually beacons (broadcasts) the SSID several times a second so that users who have WNICs can see a display of all WLANs within range of the AP’s signal.
- 7. Vendor Default SSIDs 3Com 3Com, comcomcom, 101 Apple Airport Network Belkin (54G) Belkin54g Cisco tsunami Compaq COMPAQ D-Link WLAN, default Dell wireless Intel Intel, 101, XLAN, 195, Intel Gateway Linksys linksys, wireless, linksys-g Microsoft MSHOME Netgear Wireless, Netgear SMC WLAN, BRIDGE, SMC Symantec 101 U.S. Robotics WLAN, USR9106, USR5450, USR8022, USR8054
- 8. dd-wrt DD-WRT is Linux-based firmware for wireless routers and access points . dd-wrt Linux embedded OS that replaces the embedded OS used on hundreds of routers from Linksys, D-Link, Netgear, Belkin, Microsoft, U.S. Robotics, Dell, Buffalo, and many others.
- 11. Disable SSID Broadcasting • Can use a passive wireless sniffer, such as Kismet • Kismet is a network detector, packet sniffer, and intrusion detection system for 802.11 wireless LANs. • Kismet will work with any wireless card which supports raw monitoring mode, and can sniff 802.11a, 802.11b, 802.11g, and 802.11n traffic. • Kismet is a very powerful wireless sniffing tool that is found in Kali Linux. This is an open-source tool very familiar to ethical hackers, computer network security professionals and penetration testers Unlike NetStumbler, which can pick up only broadcasted SSIDs, Kismet can detect SSIDs in WLAN client traffic.
- 12. Understanding Wireless Network Standards Standard Frequency Maximum rate Modulation method 802.11 2.4 GHz 1 or 2 Mbps FHSS/DSSS 802.11a 5 GHz 54 Mbps OFDM 802.11b 2.4 GHz 11 Mbps DSSS 802.11g 2.4 GHz 54 Mbps OFDM 802.11n 2.4 GHz 600 Mbps OFDM 802.15 2.4 GHz 2 Mbps FHSS 802.16 (WiMAX) 10–66 GHz 120 Mbps OFDM 802.20 (Mobile Wireless Access Working Group) Below 3.5 GHz 1 Mbps OFDM Bluetooth 2.4 GHz 12 Mbps Gaussian frequency shift keying (GFSK) HiperLAN/2 5 GHz 54 Mbps OFDM
- 13. Signal Modulation data to be moved over radio waves, it must be modulated on the carrier signal or channel. Modulation defines how data is placed on a carrier signal. spread spectrum modulation means data is spread across a large-frequency bandwidth instead of traveling across just one frequency band. In other words, a group of radio frequencies is selected, and the data is “spread” across this group.
- 14. Spread spectrum, the most widely used WLAN technology, uses the following methods: Frequency-hopping spread spectrum (FHSS): Data hops to other frequencies to avoid interference that might occur over a frequency band. This hopping from one frequency to another occurs at split-second intervals and makes it difficult for an intruder or attacker to jam the communication channel. Direct sequence spread spectrum (DSSS): DSSS differs from FHSS, in that it spreads data packets simultaneously over multiple frequencies instead of hopping to other frequencies. Orthogonal frequency division multiplexing (OFDM): The bandwidth is divided into a series of frequencies called tones, which allows a higher throughput (data transfer rate) than FHSS and DSSS do.
- 15. Understanding Wardriving detect access points that haven’t been secured. most APs have no passwords or security measures, so wardriving can be quite rewarding for hackers. As of this writing, wardriving isn’t illegal; using the resources of networks discovered with wardriving is, of course, a different story.
- 16. How It Works To conduct wardriving, an attacker or a security tester simply drives around with a laptop computer containing a WNIC, an antenna, and software that scans the area for SSIDs. Not all WNICs are compatible with scanning software, so you might want to look at the software requirements first before purchasing the hardware. Antenna prices vary, depending on their quality and the range they can cover. Some are as small as a cell phone’s antenna, and some are as large as a bazooka, which you might have seen in old war films. The larger ones can sometimes return results on networks miles away from the attacker. The smaller ones might require being in close proximity to the AP. Most scanning software detects the company’s SSID, the type of security enabled, and the signal strength, indicating how close the AP is to the attacker. Because attacks against WEP are simple and attacks against WPA are possible, any 802.11 connection not using WPA2 should be considered inadequately secured. The following sections introduce some tools that many wireless hackers and security professionals use.
- 17. NetStumbler For Windows that enables detecting WLANs Verifying the WLAN configuration Detecting other wireless networks that might be interfering with a WLAN Detecting unauthorized APs that might have been placed on a WLAN Another feature of NetStumbler is its capability to interface with a GPS, enabling a security tester or hacker to map out locations of all WLANs the software detects.
- 18. NetStumbler When the program identifies an AP’s signal, it logs the SSID, MAC address of the AP, manufacturer of the AP, channel on which the signal was heard, strength of the signal, and whether encryption is enabled (but not a specific encryption type).
- 19. Kismet free and runs on Linux, BSD UNIX, Mac OS X, and even Linux PDAs. The software is advertised as being more than just a wireless network detector. Kismet is also a sniffer and an intrusion detection system and Wireshark- and Tcpdump-compatible data logging Compatible with AirSnort and AirCrack Network IP range detection Detection of hidden network SSIDs Graphical mapping of networks Manufacturer and model identification of APs and clients Detection of known default AP configurations
- 20. Understanding Wireless Hacking Hacking a wireless network isn’t much different from hacking a wired LAN. Many of the port-scanning and enumeration tools you’ve learned about can be applied to wireless networks.
- 21. Tools of the Trade A wireless hacker usually has a laptop computer, a WNIC, an antenna, sniffers (Tcpdump or Wireshark, for example), tools such as NetStumbler or Kismet, and lots of patience. After using NetStumbler or Kismet to determine the network name, SSID, MAC address of the AP, channel used, signal strength, and which type of encryption is enabled, a security tester is ready to continue testing.
- 22. Tools of the Trade Wireless routers that perform DHCP functions can pose a big security risk. If a wireless computer is issued an IP address, a subnet mask, and DNS information automatically, attackers can use all the skills they learned in hacking wired networks on the wireless network. If DHCP isn’t used, attackers simply rely on Wireshark or Tcpdump to sniff packets passing through the wireless network to gather this IP configuration information. (As a security professional, you should recommend disabling DHCP on wireless networks and assigning IP addresses to wireless stations manually.) They can then configure the WNIC with the correct IP information. What do attackers or security testers do if WEP or WPA is enabled on the AP? Several tools address this issue. AirCrack NG and WEPCrack, are what prompted organizations to replace WEP with the more secure WPA as their authentication method.
- 23. AirCrack NG As a security professional, your job is to protect a network and make it difficult for attackers to break in. You might like to believe you can completely prevent attackers from breaking in, but unfortunately, this goal is impossible. AirCrack NG (included on the BackTrack files or available free at www.aircrack-ng.org) is the tool most hackers use to access WEP- enabled WLANs. AirCrack NG replaced AirSnort, a product created by wireless security researchers Jeremy Bruestle and Blake Hegerle, who set out to prove that WEP encryption was faulty and easy to crack. AirSnort was the first widely used WEP-cracking program and woke up nonbelievers who thought WEP was enough protection for a WLAN. AirCrack NG took up where AirSnort (and the slightly older WEPCrack) left off.
- 24. Countermeasures for Wireless Attacks Many countermeasure, such as using certificates on all wireless devices, are time consuming and costly. If you approach securing a wireless LAN as you would a wired LAN, you’ll have a better chance of protecting corporate data and network resources. Would you allow users to have access to network resources simply because they plugged their NICs into the company’s switch or hub? Of course not. Then why would you allow users to have access to a wireless LAN simply because they have WNICs and know the company’s SSID? If a company must use wireless technology, your job is to make it as secure as possible. Be sure wireless users are authenticated before being able to access any network resources. Here are some additional guidelines to help secure a wireless network:
- 25. Countermeasures for Wireless Attacks honeypots, which are hosts or networks available to the public that entice hackers to attack them instead of a company’s real network. To make it more difficult for wardrivers to discover your WLAN, you can use Black Alchemy Fake AP (available free at ww.blackalchemy.to/project/fakeap/). As its name implies, this program creates fake APs, which keeps war-drivers so busy trying to connect to nonexistent wireless networks that they don’t have time to discover your legitimate AP. There are measures for preventing radio waves from leaving or entering a building so that wireless technology can be used only by people in the facility. One is using a certain type of paint on the walls, but this method isn’t foolproof because some radio waves can leak out if the paint isn’t applied correctly. Use a router to filter unauthorized MAC and IP addresses and prevent them from having network access. (can spoof)